TL;DR: In a nutshell: Strac is the Intercom Redaction Solution You Need for Security & Compliance
- Customers post sensitive personal information on Intercom chats, which can lead to compliance issues and data breaches.
- Strac Intercom App is a DLP software that can detect and redact sensitive comments and attachments.
- Strac can be configured to block sensitive PII or PHI in Intercom conversations.
- Strac offers a list of sensitive data elements that are automatically pinpointed and concealed.
- Strac is available in Intercom's App Store and provides audit reports for compliance, risk, and security officers.
- Checkout our video demo below to learn about how Strac Intercom DLP and redaction works

The Consequences of Not Redacting Personal Data from Intercom
Customers post sensitive personal information (PII or PHI) on Intercom chats/conversations (Customer Support Tool) for a given business function. Some of the burning reasons on why your Intercom account needs to be protected:
- Compliance: Every day, government legislation passes Consumer Privacy laws geared to protect consumer data from malicious entities. California and Illinois have been the latest to introduce these laws, including a Biometric Information Privacy Act. For many organizations, data can be spread across a wide range of systems, which can be challenging to keep up with Privacy law enactments. It is a nightmare for companies to do manual cleanup of those sensitive messages sitting within your employee's zendesk account as deep inspection is time consuming and error-prone. At the same time, you need to stay compliant and prevent exfiltration of sensitive data.
- In the first six months of 2019, a reported 3,813 data breaches affected 4.1 billion records, an increase from 2018. Of which, 70% of leaks exposed user emails, while 65% included sensitive information revealing passwords. According to IBM, the average time it takes for an organization to identify a data breach occurred is 206 days, with an organizational cost of $3.92 million.
- Between 2018 and 2020, there was a 47% increase in insider threat incidents. This includes malicious data exfiltration and accidental data loss.
How Strac Ensures Security &Compliance with its Intercom Redaction Solution
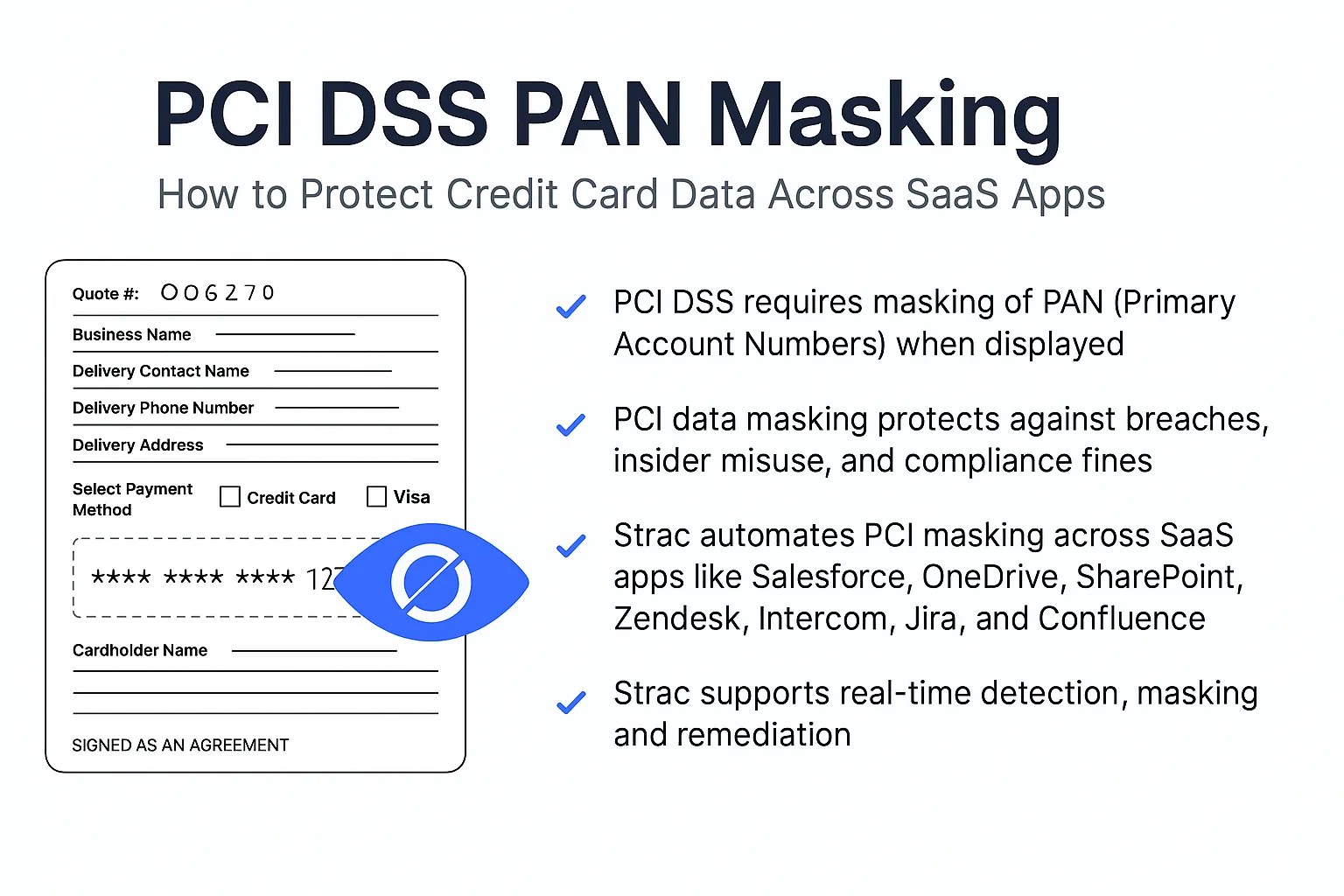
Strac Intercom App is a Data Loss Prevention (DLP) software. There are 2 modes:
- Detect Only: Once configured, it automatically discovers sensitive comments and attachments. Customers can see Findings of sensitive tickets in the Strac UI Vault and get notifications.
- Redact: Once configured, it masks (aka redacts or removes) sensitive comments and attachments while allowing authorized users to view those Intercom tickets in Strac UI Vault. With this, you will block sensitive PII or PHI in Intercom conversations.
A business can configure a list of sensitive data elements (SSN, DoB, DL, Passport, CC#, Debit Card, API Keys, etc.) to redact. Compliance, Risk and Security officers will get audit reports of who accessed which messages.
Is Strac Intercom Redaction/DLP app published on Intercom's App Store?
Yes, it is published here: https://www.intercom.com/app-store/?app_package_code=stracapp
Have a glance at Strac's assortment of sensitive data points, which are automatically pinpointed and concealed by Strac. More details at this link: https://www.strac.io/blog/strac-catalog-of-sensitive-data-elements











.webp)














.webp)







.avif)


