Microsoft Endpoint Data Loss Prevention (DLP) Guide
Modern Windows DLP for endpoints, browsers, SaaS, and GenAI. Block USB leaks, AI uploads, and insider threats with real-time data lineage and enforcement.
Windows DLP is about one thing; stopping sensitive data from leaving Windows devices.
Traditional Windows DLP focuses on endpoints; blocking USB transfers, monitoring file copies, and inspecting email attachments. That still matters. But today, most data leaves through browsers, SaaS apps, and AI tools; not just local files.
A modern Windows DLP strategy must cover copy-paste into web apps, file uploads to cloud storage, Slack messages, CRM exports, and GenAI prompts. If your Windows device connects to SaaS and AI platforms, your DLP controls need to extend beyond the operating system.
In this guide, we break down how Windows DLP works, where Microsoft-native controls fit, and what’s required to properly protect sensitive data in cloud-first environments.
Microsoft DLP lives inside Microsoft Purview and protects data across Microsoft 365 — including Microsoft Exchange, Microsoft SharePoint, Microsoft Teams, and Windows endpoints.
At its core, Microsoft DLP:
It works well inside Microsoft-controlled environments.
The issue starts when data leaves that ecosystem.
Because Windows endpoints do more than use Microsoft apps.
They use browsers.
They use AI tools.
They use third-party SaaS.
That’s where visibility thins out.
Legacy DLP solutions rely on gateway scanning and network monitoring to identify potential data leaks. But with remote workers bypassing the corporate network, these tools are blind to what users are doing on their local devices. Microsoft Endpoint DLP closes this visibility gap by applying DLP directly on endpoints.
Built natively into Microsoft 365, Endpoint DLP integrates with services like Microsoft Defender for Endpoint to provide unified data protection. Using advanced content scanning and OCR, it detects sensitive information on Windows and macOS devices. Granular policies allow you to control what actions users can take with confidential data such as copying files or printing documents.
While third-party DLP tools feel bolted onto Microsoft 365, Endpoint DLP is part of the fabric. Tight integration with Azure Active Directory and Microsoft Intune enables seamless policy enforcement and monitoring anywhere users access corporate data.

Here are some of the standout capabilities of Microsoft Endpoint Data Loss Prevention:
Create and deploy DLP policies tailored to your specific security requirements. Policies combine flexible content matching conditions like sensitive info types, file types, metadata, and exact content. Apply intelligent actions ranging from block to override to simple auditing.
For example, you may want to block copying credit card numbers to USB drives while simply auditing transfers of HIPAA data to business associates. Endpoint DLP policies support these nuanced use cases.
Endpoint DLP policies remain in force even when a device loses internet connectivity. For example, confidential files on a laptop will remain protected when offline in accordance with policy. Pending policy updates sync once the device is back online.
Before allowing users to share or distribute sensitive content, Endpoint DLP can temporarily block activities until it determines whether they comply with policy. This prevents data from leaving an endpoint before it can be secured.
Rich alerts and an interactive timeline provide insights into data vulnerabilities, policy violations, insider risk events, and other threats. Pivot seamlessly into Microsoft Defender for Endpoint for deeper investigation and response.
Microsoft Endpoint DLP policies are managed from the same Microsoft Purview portal as Microsoft 365 data loss prevention. Protection extends across Exchange, SharePoint, OneDrive, and more. Policies follow users consistently across all endpoints and cloud services.
Windows powers over 70% of enterprise desktops. That makes it the largest data exfiltration surface in most organizations. Here’s what actually happens on Windows endpoints:
Employees plug in a drive and copy gigabytes in minutes.
Sensitive files uploaded to personal Gmail, Dropbox, or AI tools over HTTPS.
Customer data pasted into ChatGPT or Copilot.
Confidential dashboards printed or screens captured.
Small transfers over months that never trigger thresholds.
.docx renamed to .jpg to bypass simple rules.
Sudden late-night bulk downloads.
Most legacy DLP tools catch one or two of these.
Modern Windows DLP must catch all of them.
Modern data leaves through encrypted browser sessions.
Strac decrypts and re-encrypts SSL traffic locally on the endpoint to inspect:
Employees are uploading:
into:
Modern Windows DLP must:
Legacy DLP vendors weren’t built for this.
Strac was build with GenAI DLP in mind!
Content-only scanning isn’t enough.
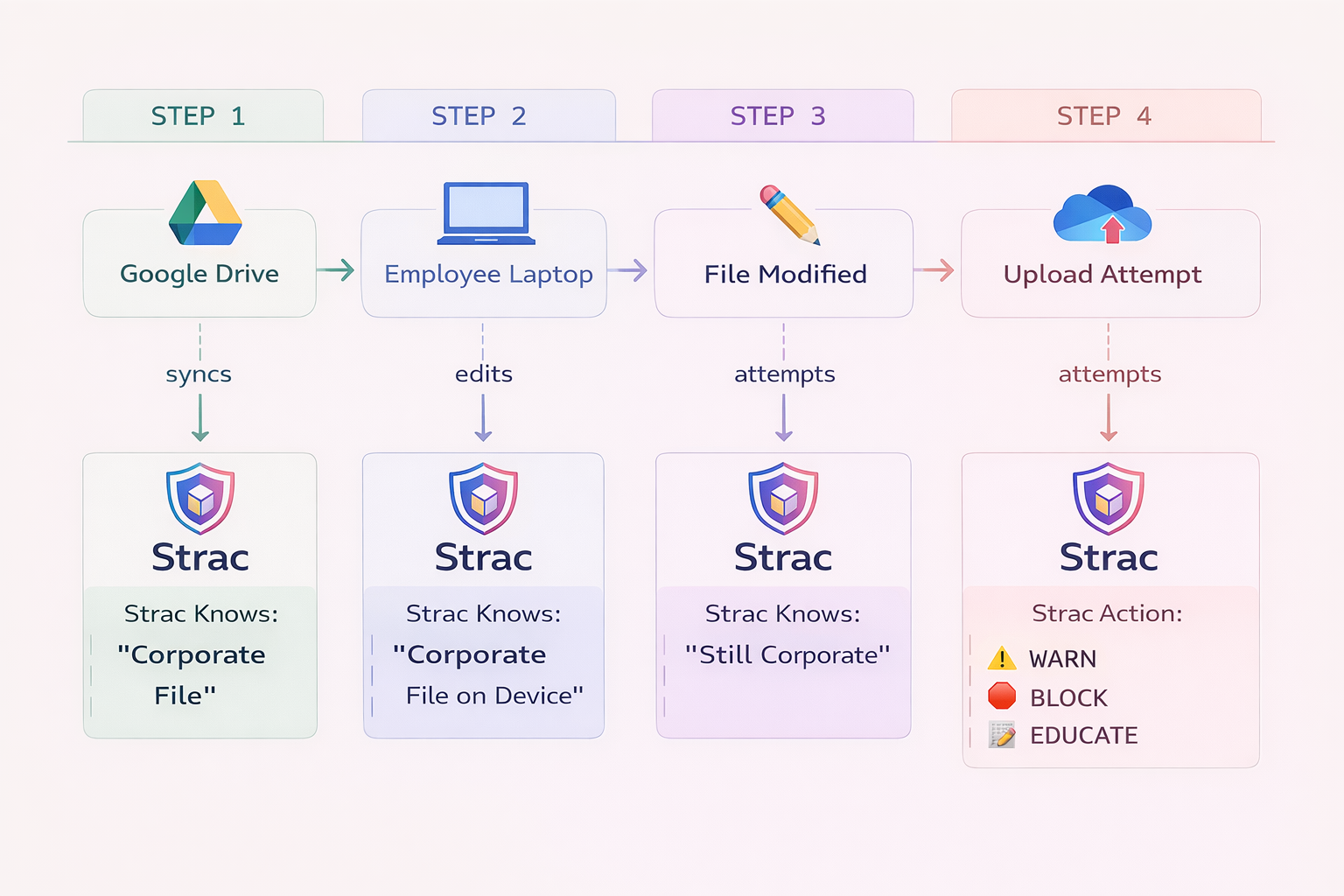
If someone downloads a file from SharePoint, renames it, edits it, and uploads it — traditional DLP sees a “new file.”
Strac tracks lineage.
This is how you stop intentional insider exfiltration.
Not just accidents.
Not every breach is loud.
Strac builds behavioral baselines per user and flags:
This is insider risk detection built into Windows DLP.
Not bolted on later.
Most DLP tools ignore:
Strac enforces policy before these actions complete.
Because screenshots are still data exfiltration.
Microsoft Endpoint DLP is strong inside Microsoft 365.
But Windows endpoints don’t live only in Microsoft.
Security leaders consistently run into:
If you operate in a hybrid SaaS + AI environment, you need more than ecosystem-bound DLP.
Follow these best practices when deploying Microsoft Endpoint DLP:
Confirm licensing requirements - Endpoint DLP requires premium Microsoft 365 licenses including E5, A5, E5 Compliance, and A5 Compliance.
Onboard devices - Use tools like Microsoft Intune to deploy the Endpoint DLP agent to your Windows and macOS devices. This registers devices for monitoring.
Classify sensitive data - Identify regulated data like HIPAA or PII you need to monitor and protect. Endpoint DLP includes over 100 sensitive information types out of the box.
Develop data protection policies - Create policies aligned to your regulatory and business data security requirements tailored to your unique environment.
Educate end users - Train employees on proper data handling and make them aware of DLP monitoring to improve compliance.
Monitor policy effectiveness - Use alerts and dashboards to measure policy outcomes and fine-tune rules to maximize protection.
Remediate issues - Leverage built-in workflows to quickly investigate and resolve policy violations or insider risk incidents.
Regularly review policies - Update rules to account for new regulations, data types, user behaviors, and other changes that occur over time.

Strac Windows DLP is designed for how data actually moves today; across browsers, SaaS apps, AI tools, USB devices, and local endpoints. It goes beyond basic file monitoring to deliver real-time enforcement at the Windows device level, with deep SSL inspection, GenAI upload protection, corporate data lineage tracking, behavioral anomaly detection, and print and screenshot controls. Instead of just alerting after data leaves, Strac blocks, encrypts, quarantines, or warns in real time; stopping exfiltration before it happens. It’s lightweight, fast to deploy, and built for cloud-first, AI-driven enterprises.
Learn more about how Strac can enhance your Microsoft Endpoint DLP strategy by exploring our comprehensive DLP solutions.
With remote work accelerating, legacy network-centric security models are no longer sufficient. Microsoft Endpoint Data Loss Prevention enables intelligent protection of sensitive information directly on user devices. Before confidential data can leave an endpoint, granular policies ensure it is handled properly.
To learn more about maximizing data protection with Microsoft Endpoint DLP, contact your Microsoft sales representative for a personalized demonstration. In today's decentralized work environment, resilient endpoint security is critical - and Microsoft Endpoint DLP delivers.
Ready to take your data protection strategy beyond Microsoft Endpoint DLP? Book a demo with Strac today to discover how our advanced DLP solution can provide comprehensive protection across your entire digital ecosystem.
Endpoint DLP requires a premium license such as E5, A5, E5 Compliance, or A5 Compliance. More basic Office 365 licenses do not include it.
Endpoint DLP can monitor over 50 different activities including copy, move, print, email send, and upload to cloud services. Policies can be set to block, audit, or override these activities.
Yes, optical character recognition capabilities allow Endpoint DLP to scan images such as JPEGs and identify sensitive text or data points.
Endpoint DLP supports macOS devices and has limited iOS and Android support. Enrollment in Intune MDM is required for mobile device management.
Absolutely. Endpoint DLP includes over 100 pre-built sensitive information types covering categories like HIPAA, PII, PCI, and GDPR. Custom types can also be created.
.avif)
.avif)
.avif)
.avif)
.avif)






.gif)

